Pyramid of Pain
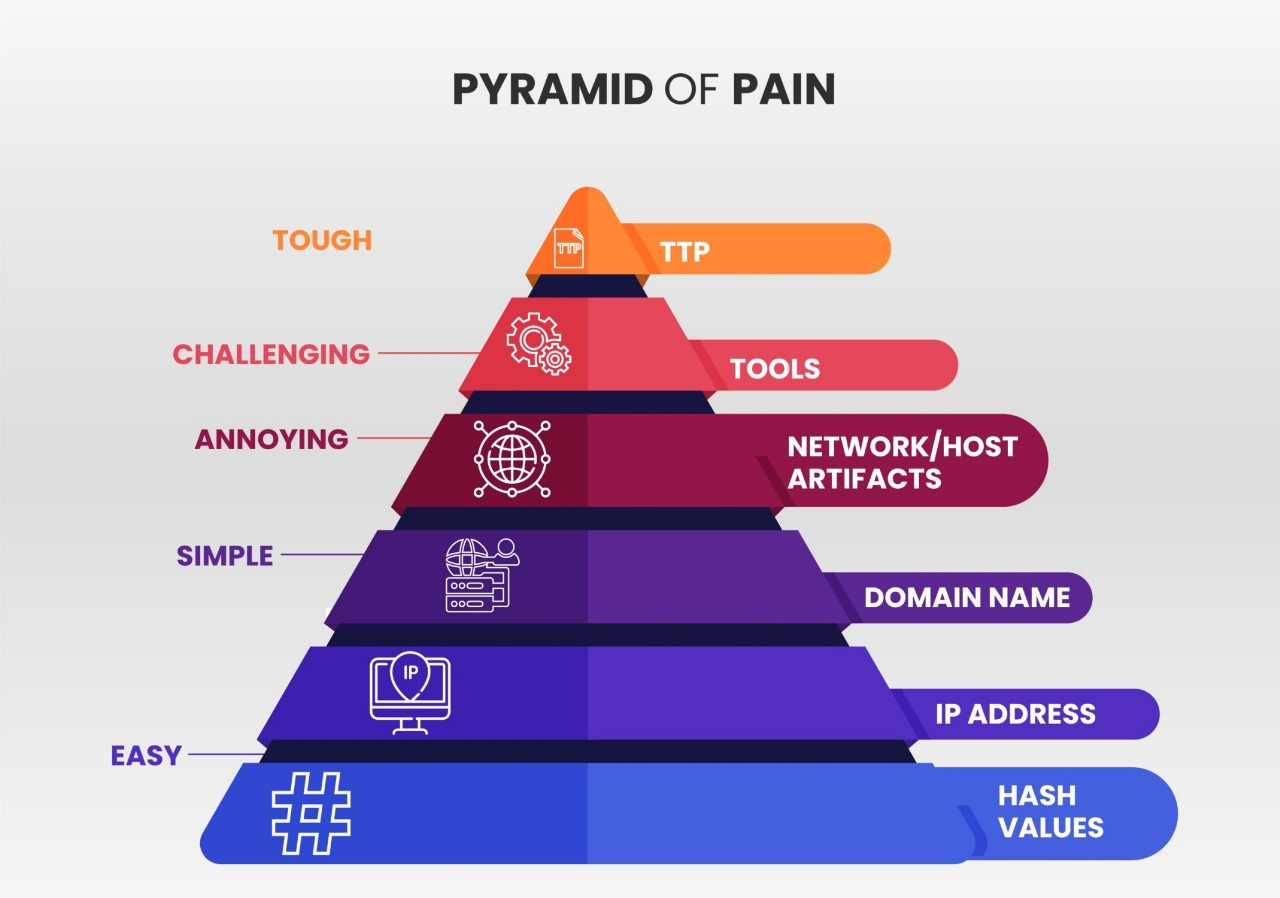
The Pyramid of Pain shows that the lower an indicator is, the easier it is for an attacker to change. The higher it is, the more painful it is for the attacker to adapt.
1) Hash Values — Trivial
Definition
A hash value is a unique fingerprint of a file.
Examples
- MD5:
44d88612fea8a8f36de82e1278abb02f - SHA-256 hash of a malware sample
Use case
A SOC analyst finds a known malicious file hash in EDR or email attachment logs and blocks or quarantines that exact file.
How a SOC analyst should think and use it
Hashes are useful for quick confirmation of known malware, but weak for long-term defense. If the attacker changes even one byte in the file, the hash changes.
Use hashes for:
- Fast blocking
- Historical searching
- Confirming known bad files
Do not rely on hashes alone.
2) IP Addresses — Easy
Definition
An IP address identifies a device on a network.
Examples
185.220.101.4545.77.12.9
Use case
A SOC analyst sees several hosts reaching out to a suspicious external IP linked to command-and-control traffic and blocks it at the firewall.
How a SOC analyst should think and use it
IPs are useful, but attackers can rotate them, use cloud servers, VPNs, or proxies. An IP hit is a good lead, not always the full answer.
Use IPs for:
- Alert triage
- Firewall blocking
- Threat hunting across logs
Always ask: What domain, process, user, or behavior is tied to this IP?
3) Domain Names — Simple
Definition
A domain name is the human-readable name used to reach a resource on the internet.
Examples
login-microsoft-support.comupdate-securebank.net
Use case
A SOC analyst detects users trying to access a lookalike phishing domain and blocks it through DNS filtering or secure web gateway controls.
How a SOC analyst should think and use it
Domains are stronger than raw IPs because attackers often care about keeping a phishing or malware domain alive. Still, they can register new ones.
Use domains for:
- Phishing detection
- DNS monitoring
- Identifying malicious infrastructure
Think beyond one domain. Ask: Are there similar domains, subdomains, or DNS patterns?
4) Network / Host Artifacts — Annoying
Definition
Artifacts are traces attackers leave behind on systems or networks during activity.
Examples
- A registry Run key for persistence
- A PowerShell command spawning from Word
- An unusual HTTP user-agent string
- A file dropped in
AppData\Roaming
Use case
A SOC analyst hunts for a malware pattern where winword.exe launches powershell.exe, then a file appears in a temp directory and a network connection follows.
How a SOC analyst should think and use it
Artifacts are much better than simple indicators because they show how the attack behaved, not just what one file or IP was.
Use artifacts to:
- Build detections
- Investigate scope
- Connect related alerts
Think in chains: parent process → child process → file change → network call
5) Tools — Challenging
Definition
Tools are the software or utilities attackers use to perform actions.
Examples
- Mimikatz
- Cobalt Strike
- PsExec used suspiciously
Use case
A SOC analyst detects signs of a known post-exploitation tool being used on multiple hosts and responds before privilege escalation or lateral movement spreads further.
How a SOC analyst should think and use it
Tool detection hurts attackers more because changing tools takes effort. But some tools are dual-use and can also be used legitimately by admins.
Use tools as:
- Strong enrichment
- Investigation pivots
- High-confidence detection when paired with context
Do not alert only on the tool name. Ask: Who ran it, from where, on what host, and for what purpose?
6) TTPs — Tough
Definition
TTPs are Tactics, Techniques, and Procedures: the attacker’s goals, methods, and way of operating.
Examples
- Spearphishing attachment for initial access
- Credential abuse followed by lateral movement using remote access methods
Use case
A SOC analyst notices a pattern: phishing email, malicious script execution, PowerShell download, credential dumping, then remote logins to other systems. Even if the malware changes, the attack pattern is still visible.
How a SOC analyst should think and use it
This is the strongest level because it focuses on behavior and tradecraft. Attackers can swap files, IPs, and domains, but changing their whole operating style is much harder.
Use TTPs for:
- Durable detections
- Threat hunting
- Mapping activity to MITRE ATT&CK
- Understanding the bigger incident story
Think like this: What is the attacker trying to achieve, and what sequence of behaviors shows that?
Key Lesson for a SOC Analyst
A good SOC analyst should not stop at the bottom of the pyramid.
- Hashes, IPs, and domains help with quick detection and blocking.
- Artifacts, tools, and TTPs help you understand the intrusion and build stronger detections.
Best mindset
Use low-level indicators to find the attack. Use higher-level behavior to truly defend against it.